Standard smartphones fail under loss, seizure, or coercion, risking data exposure. Privacy Devices' hardened systems, GrapheneOS, duress PINs, and metadata minimisation protect users in high-risk scenarios like journalism and...
Duress PIN solutions provide executives and investigators with covert device access control, panic actions, decoy profiles, metadata minimisation, and role-based presets to protect data and ensure post-event integrity.
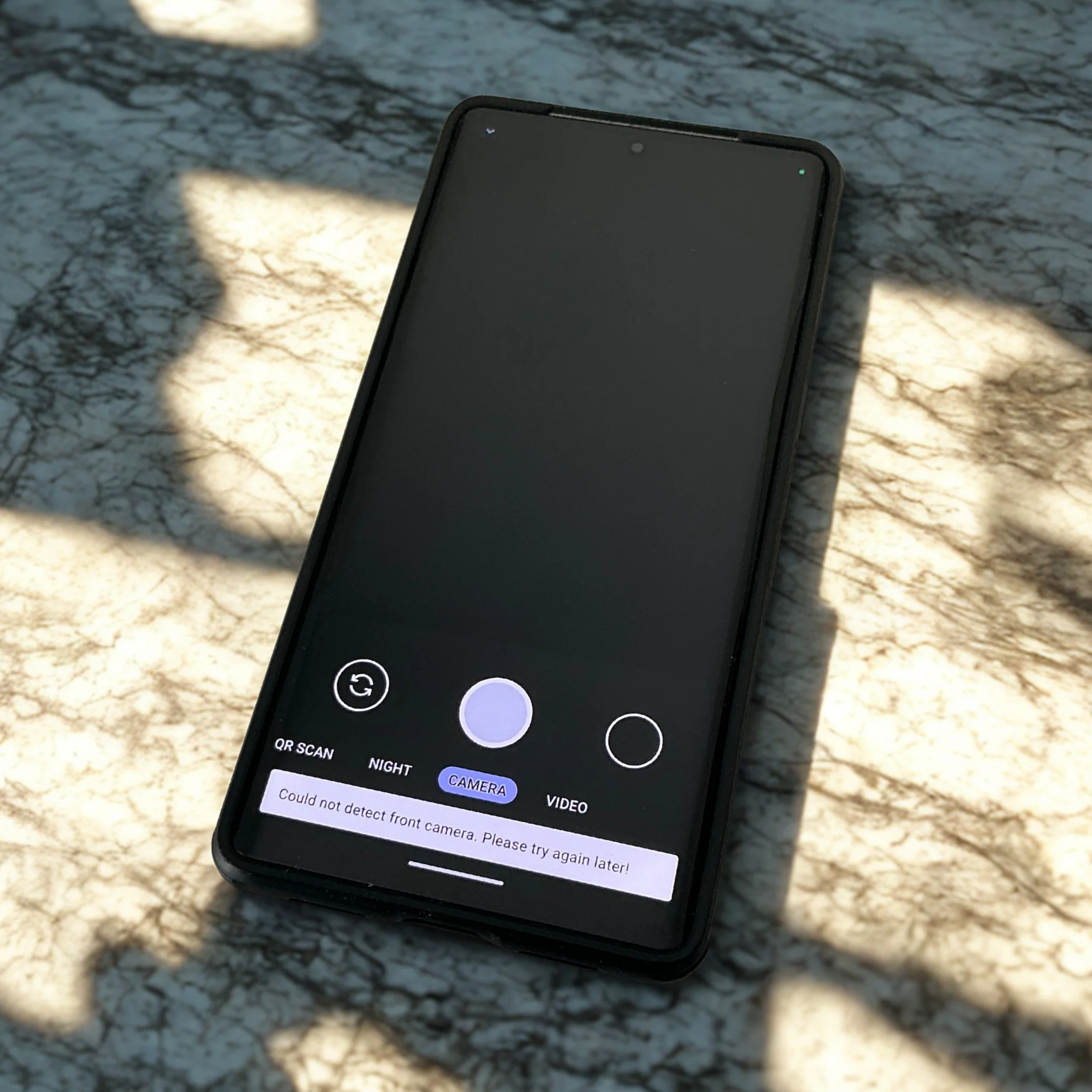
Fail-closed device failure modes and features like duress PINs, panic actions, hardened OS (GrapheneOS), metadata minimization, and secure communications protect sensitive data in high-risk situations.
Secure phones must fail safely under duress using duress PINs, panic actions, metadata minimisation, and hardened systems like GrapheneOS to protect data from coercion, seizure, and real-world threats.
Privacy Devices offers custom-built GrapheneOS phones with advanced security features—duress PINs, panic actions, metadata minimisation, compartmentalised profiles, baseband isolation—to protect executives, journalists, and investigators in high-risk environments.
Standard smartphones lack security under pressure, risking data exposure during loss, seizure, or coercion. Hardened mobile systems with duress PINs, panic actions, encryption, and metadata minimisation better protect high-risk...
Panic actions like duress PINs, instant wipes, remote lockdown, radio kill switch, and decoy profiles protect your phone and data under coercion or loss. Hardened OS and metadata minimisation...
Panic actions enable instant, local cryptographic key destruction for immediate data lockdown without cloud reliance. Privacy Devices integrates hardware-backed security, duress PINs, and hardened OS for robust, offline protection...
Custom mobile security for executives and investigators uses hardened AOSP/GrapheneOS, duress PINs, metadata minimisation, and tailored threat models to protect data under loss, seizure, or coercion.
Private mobile security consultations provide tailored, coercion-resistant setups using threat modeling, metadata minimization, secure OS like GrapheneOS, and tools like Mullvad VPN to protect sensitive data in real-world risks.