Secure phones must fail safely under duress using duress PINs, panic actions, metadata minimisation, and hardened systems like GrapheneOS to protect data from coercion, seizure, and real-world threats.
Privacy Devices offers custom-built GrapheneOS phones with advanced security features—duress PINs, panic actions, metadata minimisation, compartmentalised profiles, baseband isolation—to protect executives, journalists, and investigators in high-risk environments.
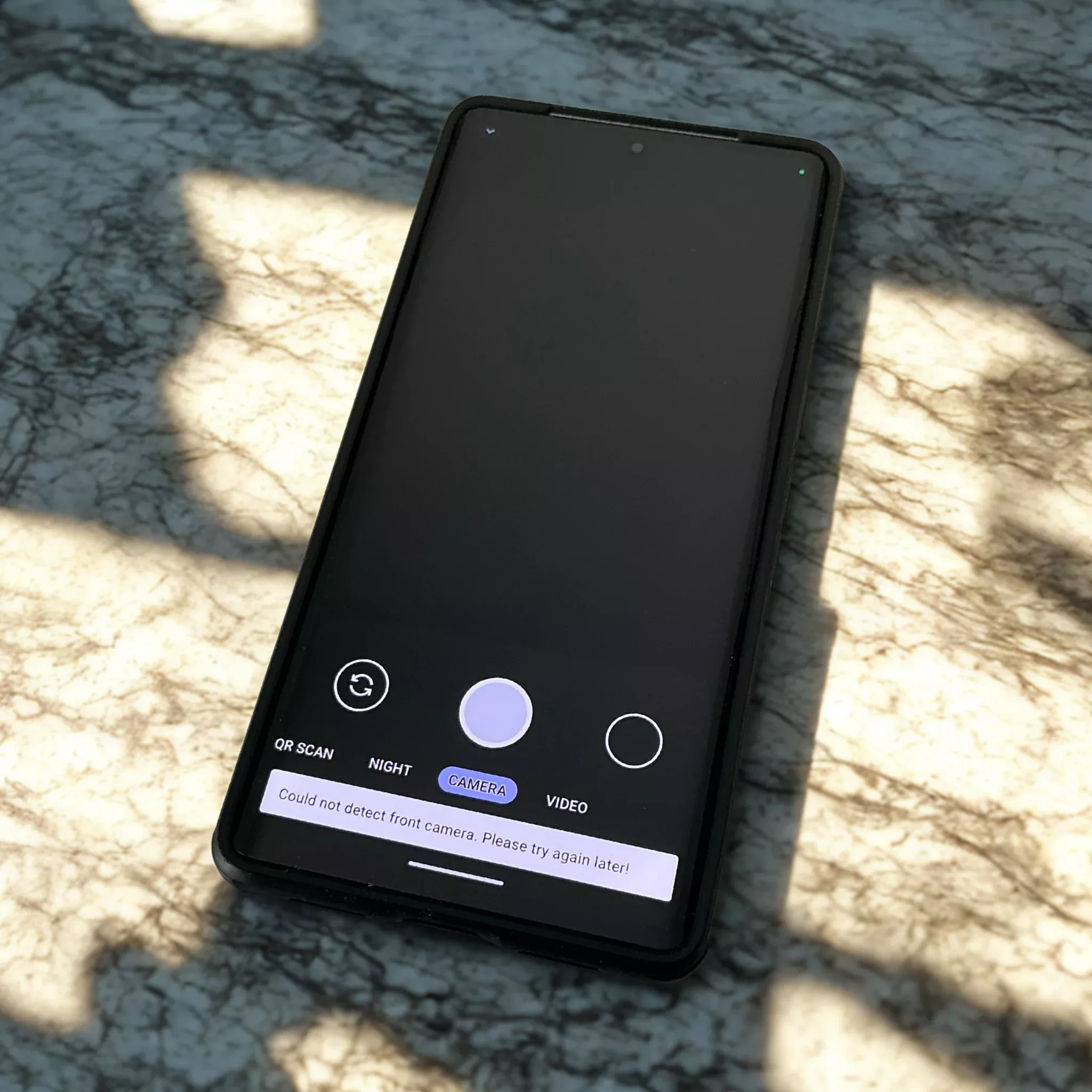
Standard smartphones lack security under pressure, risking data exposure during loss, seizure, or coercion. Hardened mobile systems with duress PINs, panic actions, encryption, and metadata minimisation better protect high-risk...
Panic actions like duress PINs, instant wipes, remote lockdown, radio kill switch, and decoy profiles protect your phone and data under coercion or loss. Hardened OS and metadata minimisation...
Standard smartphones lack protections against loss, seizure, coercion, SIM swaps, and forensic attacks. Hardened, open-source devices with duress PINs and metadata minimization offer superior real-world digital security.
Custom mobile security for executives and investigators uses hardened AOSP/GrapheneOS, duress PINs, metadata minimisation, and tailored threat models to protect data under loss, seizure, or coercion.
Duress PINs and panic actions are vital for mobile security, protecting data under coercion via secret codes and selective or full data wipes. GrapheneOS and tailored threat models enhance...
Hardened mobile systems protect data under threats like loss, seizure, and coercion via duress PINs, hardware-backed encryption, metadata minimisation, verified boot, and tailored security for high-risk users.
This guide details mobile strategies for privacy-critical professionals, emphasizing metadata risks and mitigation via hardened systems like GrapheneOS, duress PINs, panic actions, and privacy-focused devices.
Custom security configurations for privacy-critical professionals create hardened phones that protect data under duress via features like duress PINs, metadata minimisation, verified boot, and remote wipe, ensuring secure use...