Standard smartphones fail under loss, seizure, or coercion, risking data exposure. Privacy Devices' hardened systems, GrapheneOS, duress PINs, and metadata minimisation protect users in high-risk scenarios like journalism and...
Hardened mobile systems protect data during seizure and coercion using duress PINs, metadata minimisation, verified boot, and network hardening, ensuring privacy in high-risk scenarios.
Metadata reveals smartphone users' habits, locations, and contacts, exposing them to risks. Hardened mobile systems and strategies like encrypted communication, VPNs, and duress PINs effectively minimize this threat.
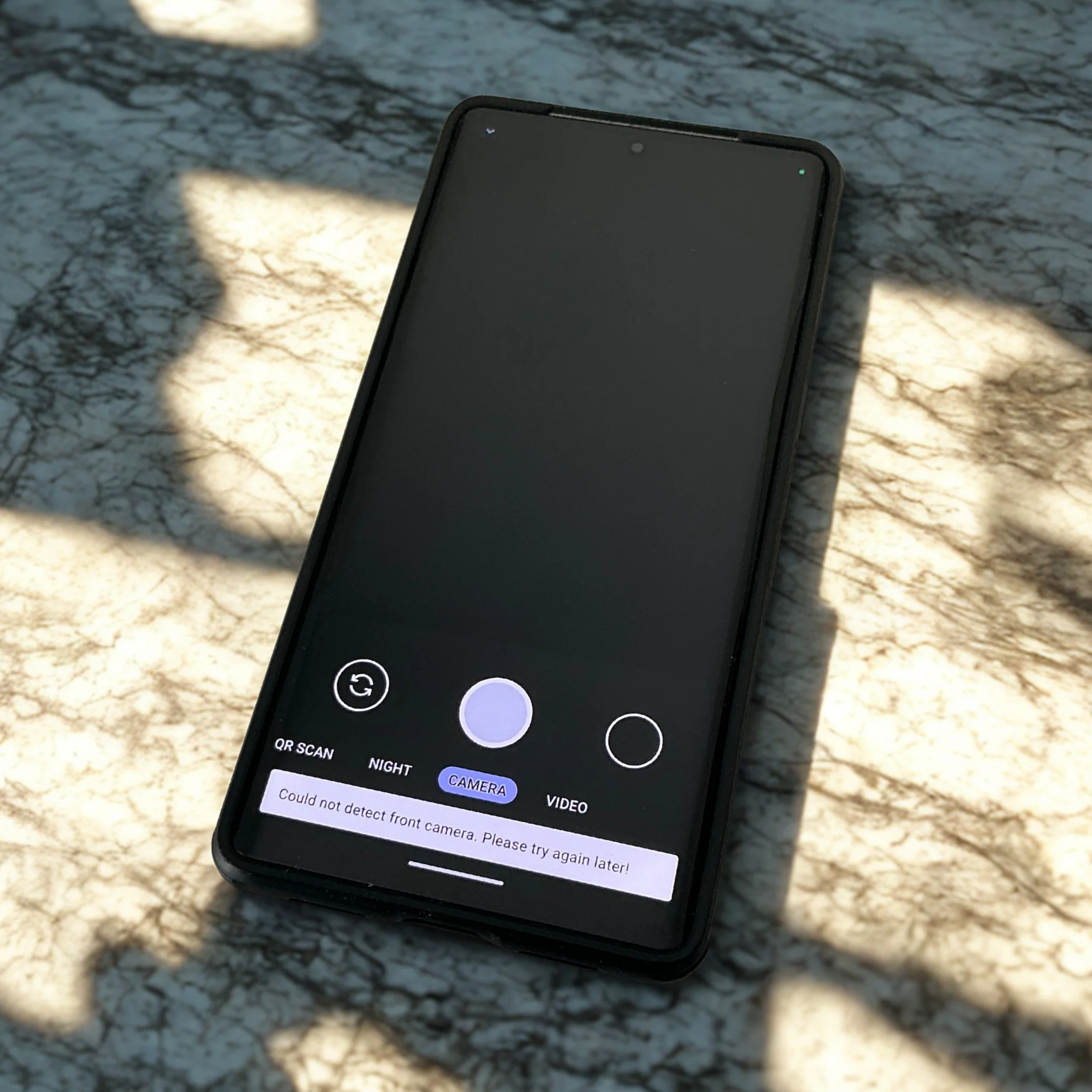
Standard smartphones lack security under pressure, risking data exposure during loss, seizure, or coercion. Hardened mobile systems with duress PINs, panic actions, encryption, and metadata minimisation better protect high-risk...
Custom mobile security for executives and investigators uses hardened AOSP/GrapheneOS, duress PINs, metadata minimisation, and tailored threat models to protect data under loss, seizure, or coercion.
Hardened mobile systems protect data under threats like loss, seizure, and coercion via duress PINs, hardware-backed encryption, metadata minimisation, verified boot, and tailored security for high-risk users.
Private mobile security consultations provide tailored, coercion-resistant setups using threat modeling, metadata minimization, secure OS like GrapheneOS, and tools like Mullvad VPN to protect sensitive data in real-world risks.
Custom security configurations for privacy-critical professionals create hardened phones that protect data under duress via features like duress PINs, metadata minimisation, verified boot, and remote wipe, ensuring secure use...
Hardened mobile systems ensure executive security via verified boot, hardware encryption, duress PINs, multi-profile separation, GrapheneOS hardening, metadata minimisation, secure communications, physical seizure defence, privacy-respecting monitoring, and local support.
Duress PINs provide irreversible data protection by instantly destroying cryptographic keys under coercion, safeguarding sensitive info via panic actions and metadata minimisation for enhanced device security.