This guide details fail-safe mobile security measures—duress PINs, panic actions, metadata minimisation, compartmentalised profiles, USB restrictions, Mullvad VPN, encryption, fake profiles, and Faraday bags—to protect data from loss, seizure,...
This guide details best practices for mobile data protection under coercion, highlighting duress PINs, panic actions, metadata minimisation, multi-profile separation, Faraday bags, SIM hygiene, AOSP hardening, GrapheneOS, secure boot,...
Critical features for hardened mobile systems include verified boot, hardware-backed keystore, strong encryption, coercion resistance, compartmentalisation, metadata minimisation, sensor governance, secure recovery, quick actions, offline protection, and tailored configurations...
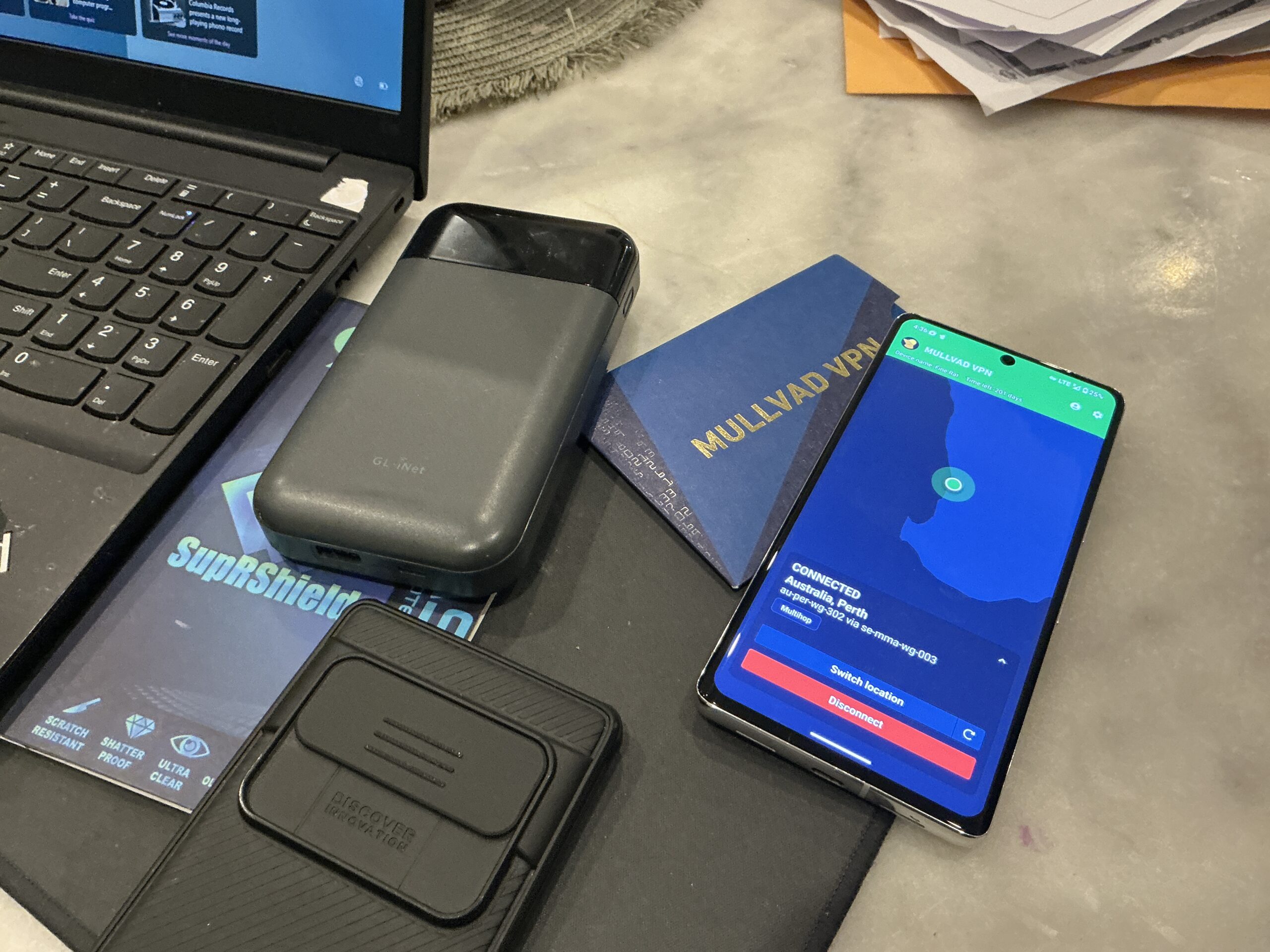
Metadata minimisation protects privacy by limiting data traces like contacts, locations, and patterns. Using compartmentalisation, VPNs, duress PINs, and open-source OS like GrapheneOS enhances security in hostile digital environments.
Duress PINs provide covert defense during device seizure by triggering panic actions like wipes or lockdowns. Hardened systems (GrapheneOS, AOSP) enhance coercion resistance tailored to threat models.
Panic Actions enable instant data lockdown via duress PINs or triggers, protecting sensitive info in high-risk situations through cryptographic key destruction, compartmentalization, and device hardening.
Custom hardened mobile setups like GrapheneOS enhance journalist and privacy pro resilience by using duress PINs, metadata minimisation, compartmentalisation, and secure communications to protect data under coercion or seizure.
Duress PIN solutions provide executives and investigators with covert device access control, panic actions, decoy profiles, metadata minimisation, and role-based presets to protect data and ensure post-event integrity.
Fail-closed device failure modes and features like duress PINs, panic actions, hardened OS (GrapheneOS), metadata minimization, and secure communications protect sensitive data in high-risk situations.
Hardened mobile systems protect data during seizure and coercion using duress PINs, metadata minimisation, verified boot, and network hardening, ensuring privacy in high-risk scenarios.