Secure your mobile against loss, seizure and coercion: a best‑practice playbook
Standard smartphones aren’t built to hold up when your device is lost, seized, or you’re forced to surrender it under pressure. Your mobile holds more than just calls and texts—it carries sensitive data that can destroy careers or compromise safety if exposed. This playbook lays out a tested framework for mobile security that includes device seizure protection, duress PINs, and metadata minimisation. If you need a system that stays secure in real-world threats, keep reading. For more information on mobile security practices, visit this guide.
Protecting Mobile Devices from Threats
Your mobile phone is more than a gadget; it’s a vault of sensitive information. Ensuring its security under all conditions is crucial.
Understanding Mobile Security Risks
Mobile security risks are all around us. Every time you use your phone, it could be exposed to threats. Imagine your data being accessed without your knowledge. This isn’t just a risk; it’s a reality for many. Mobile security involves understanding these risks and taking steps to protect against them. From hackers trying to steal your information to being forced to give up your phone, the dangers are real. Think about it: what would happen if someone got hold of your data? You need to be aware of the risks to guard against them.
Implementing Device Seizure Protection
When your device is seized, your information can be at risk. Think of device seizure protection as a digital shield. It ensures that even if your phone is taken, your data stays safe. Many people think their phone settings are enough. But in reality, they might not be. Secure configurations can make a huge difference. Add layers of protection so that even in tough situations, your data remains yours. Setting up these protections can give you peace of mind.
Enhancing Coercion Resistance
Coercion can happen unexpectedly. Imagine being pressured to unlock your phone. Without proper safeguards, your data could be exposed. This is where coercion resistance comes into play. Setting up features like duress PINs means you have a plan if forced to unlock your device. This isn’t just about security; it’s about empowerment. You maintain control even when things get tense. The longer you wait to set these up, the more you risk. So, act now to protect yourself. Learn more about mobile security and how to implement these measures today.
Key Configurations for Privacy Phones
To ensure maximum security, certain configurations are essential. These adjustments can prevent unwanted access and safeguard your privacy.
The Role of Duress PINs and Panic Actions
Duress PINs are secret passwords you use if forced to unlock your phone. Once entered, they trigger panic actions that can lock or wipe your device. This is a game-changer. Why? Because it gives you control. Most people think their regular PINs are enough, but they’re not. When things get tricky, a duress PIN can save your data. Setting one up is simple but effective. Remember, in high-pressure scenarios, preparation is your best defence.
Importance of Metadata Minimisation
Metadata might seem minor, but it can reveal a lot about you. Metadata minimisation reduces the data your phone shares. Consider this: every time you use your phone, small pieces of data get logged. This can include your location, contacts, and more. While content is protected, this peripheral data can still expose you. Minimising metadata means fewer traces of your activity. It’s like leaving a lighter footprint. This step is crucial for true privacy.
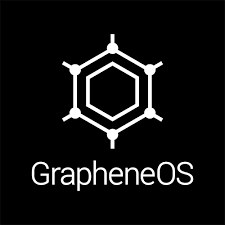
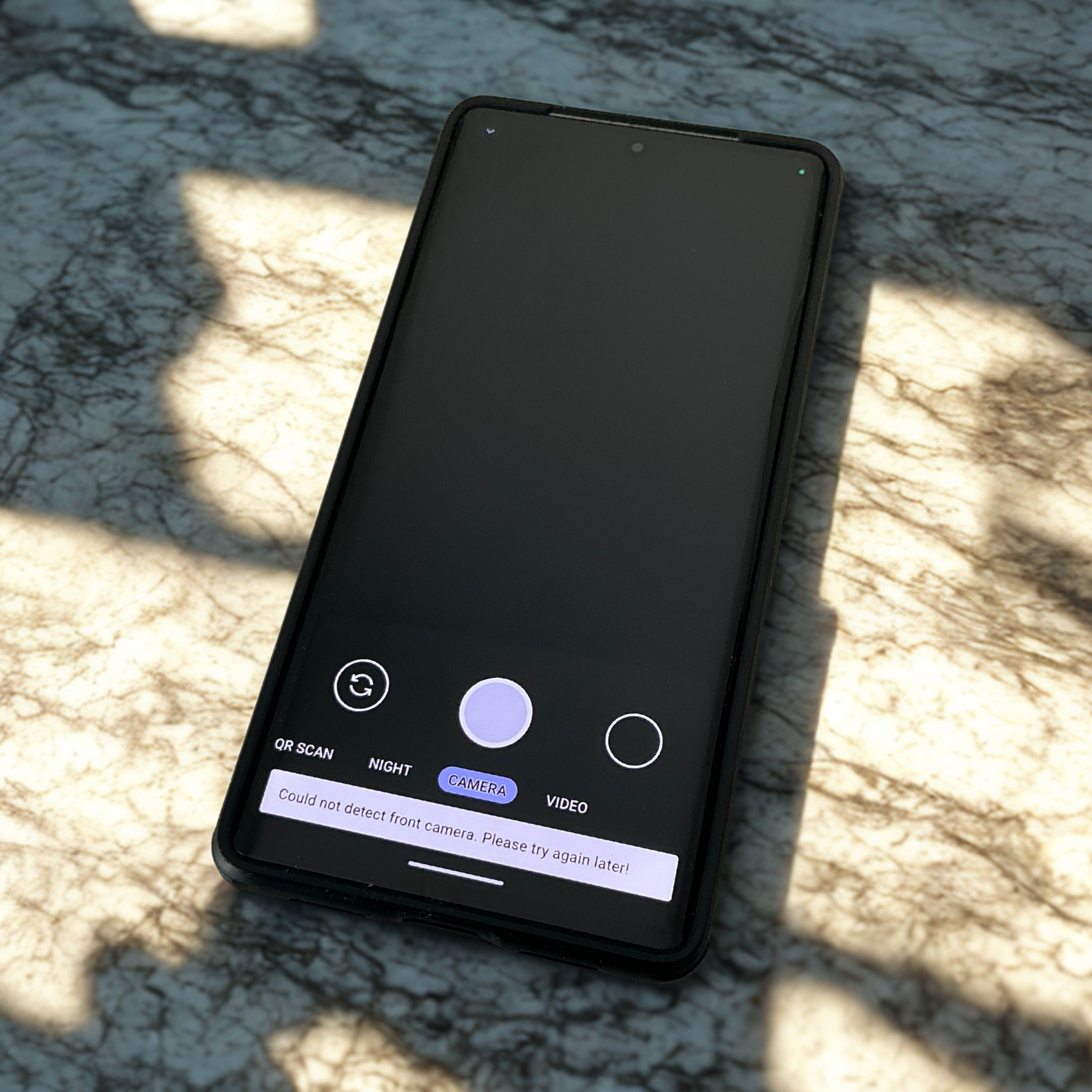
Benefits of AOSP Hardening and GrapheneOS
AOSP hardening and GrapheneOS offer robust security for your phone. They provide a foundation that’s more secure than standard Android systems. By choosing these, you’re opting for enhanced protection. The benefits? Better data integrity and fewer vulnerabilities. Many assume their current settings are enough, but they aren’t. With these systems, you gain a fortified defence. This isn’t just a recommendation; it’s a necessity for those who value privacy.
Best Practices for High-Stakes Environments
In high-pressure situations, certain practices can make all the difference. Adopting these can safeguard your data when stakes are high.
Secure Communications and SIM Hygiene
Communication is key, but so is its security. Ensuring secure communications means using encrypted messaging apps and being cautious. SIM hygiene is about managing your SIM card responsibly. This includes being alert about SIM swaps and using security locks. Most think their current practices are enough, but they’re not. By upgrading your approach, you ensure your conversations and data remain private.
Air-Gapped Backups and Full-Disk Encryption
Backups are essential, but they must be secure. Air-gapped backups are stored offline, reducing risk. In case of a breach, your data remains safe. Full-disk encryption protects every bit of your device. This means even if accessed, your data stays encrypted. Many skip these steps, thinking they’re tedious. Yet, they are crucial for total security. Implementing these measures ensures all your bases are covered.
Tailored Privacy Devices for Australian Needs
Australia has unique privacy needs. Tailored privacy devices cater specifically to these requirements. They offer configurations that address local concerns. From secure networks to region-specific threats, these devices are built for Australians. Generic solutions might miss crucial elements. By choosing tailored options, you get a fit-for-purpose solution. This isn’t just a recommendation; it’s a must for those serious about privacy. For more on device security, check out this resource.
In conclusion, securing your mobile device is essential in today’s world. By understanding risks, implementing protective measures, and adopting best practices, you can ensure your data remains safe. Prioritise these steps and take control of your digital privacy today.