Why Standard Smartphones Fail in Real‑World Privacy Threats
Standard smartphones fail when it matters most—under loss, seizure, coercion, or monitoring. Your data leaks quietly, exposing sensitive details to prying eyes and hostile forces. This isn’t about avoiding surveillance; it’s about surviving high-risk scenarios with hardened mobile systems designed for real-world pressure. In this post, you’ll learn why typical devices fall short and how tools like GrapheneOS security and duress PINs protect privacy phone users across Australia. Learn more here.
Smartphone Privacy Failures
When your smartphone isn’t built for pressure, your data is at risk. Let’s dig into how these devices can fail you.
Data Leakage Under Loss
Losing your smartphone can feel like losing a part of yourself. But the real danger isn’t just the physical loss. It’s what happens to your data. Standard devices are not equipped to protect your information when they fall into the wrong hands. Your photos, messages, and sensitive files can be accessed with little effort. Most people think their phones are safe with a simple lock screen, but that’s a risky assumption.
Consider this: Nearly 3 million smartphones are lost or stolen each year. Without proper safeguards, the data on those devices is free for the taking. This is where a privacy-focused phone shines. These devices ensure that data is encrypted and inaccessible without your permission. So even if you lose your phone, your private information stays private.
Vulnerabilities During Seizure
Imagine your phone is seized at a checkpoint or during a security sweep. The contents are often easily exploited by those who know what they’re doing. Many believe that standard privacy settings are enough, but they aren’t. A typical smartphone can reveal much more than you intend.
When your device is seized, the clock starts ticking. Every second without proper protection increases the risk of data exposure. A seizure-safe phone acts differently. It safeguards your information, even under direct threat. With features like verified boot and secure configurations, these phones are your best line of defence against unwanted access.
Coercion and Monitoring Risks
In some situations, you’re forced to unlock your phone. It could be a border officer or even a suspicious partner. Standard devices leave you vulnerable in these scenarios. You might think your password is enough, but coercion can quickly break that barrier.
Here’s the key insight: A coercion-resistant smartphone offers panic actions that shield your data when under duress. For example, entering a specific PIN could automatically lock down sensitive information. This ensures that even under pressure, your privacy remains intact. Most people aren’t aware of these solutions, but they can be a game-changer.
Privacy Devices’ Solutions

To counter these threats, Privacy Devices offers tailored solutions. Let’s explore how these systems work to protect your data.
Hardened Mobile Systems Features
A privacy phone must be robust, yet flexible. Hardened mobile systems provide this balance. They are designed with AOSP hardening and GrapheneOS security, ensuring every layer of your device is fortified.
These systems are not just about locking your phone; they are about creating a fortress around your data. With features like sensor and network lockdown, you control what information is shared and when. Every element is crafted to provide peace of mind, knowing your data is secure. This approach is not just a trend, but a necessity for anyone dealing with sensitive information.
Duress PIN and Panic Actions
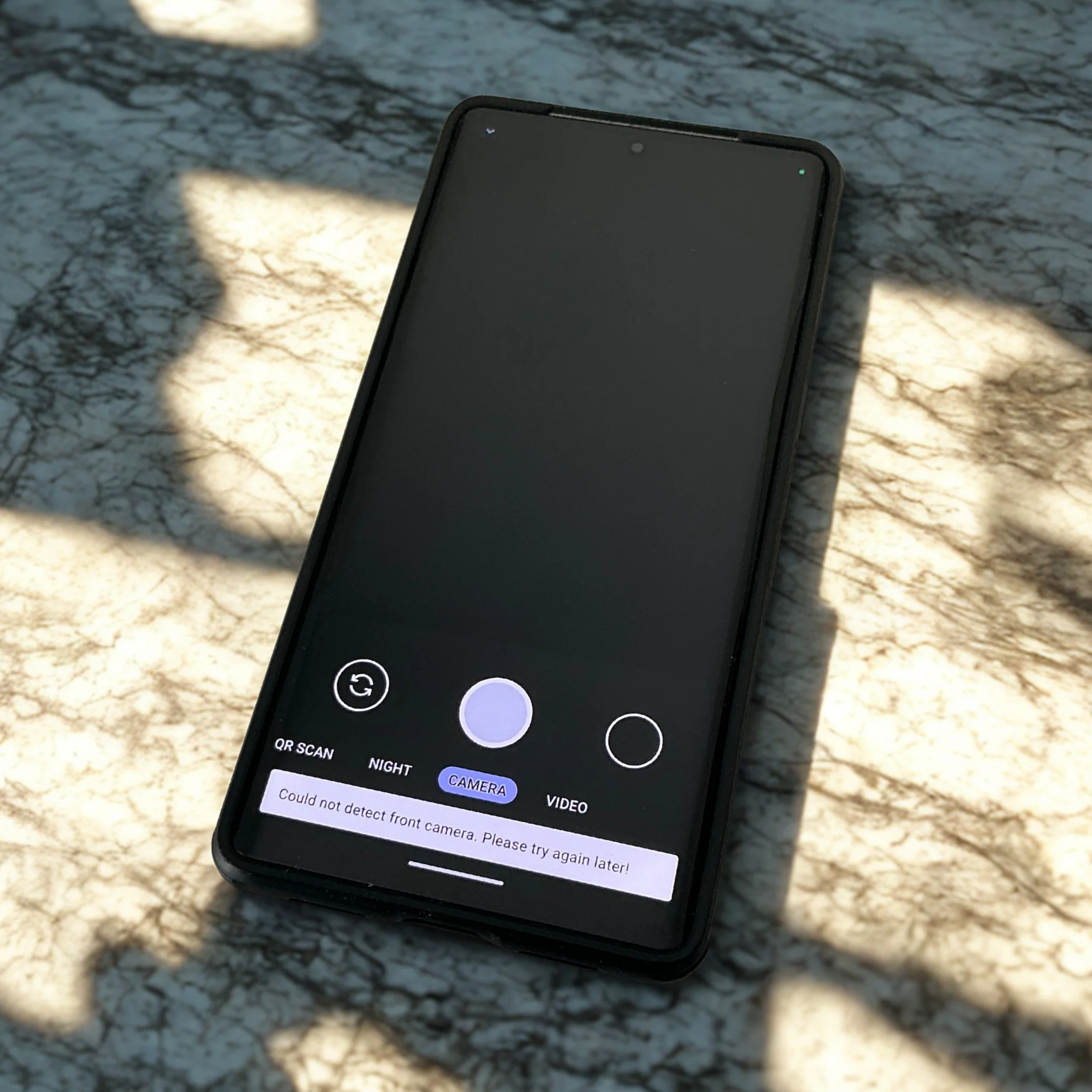
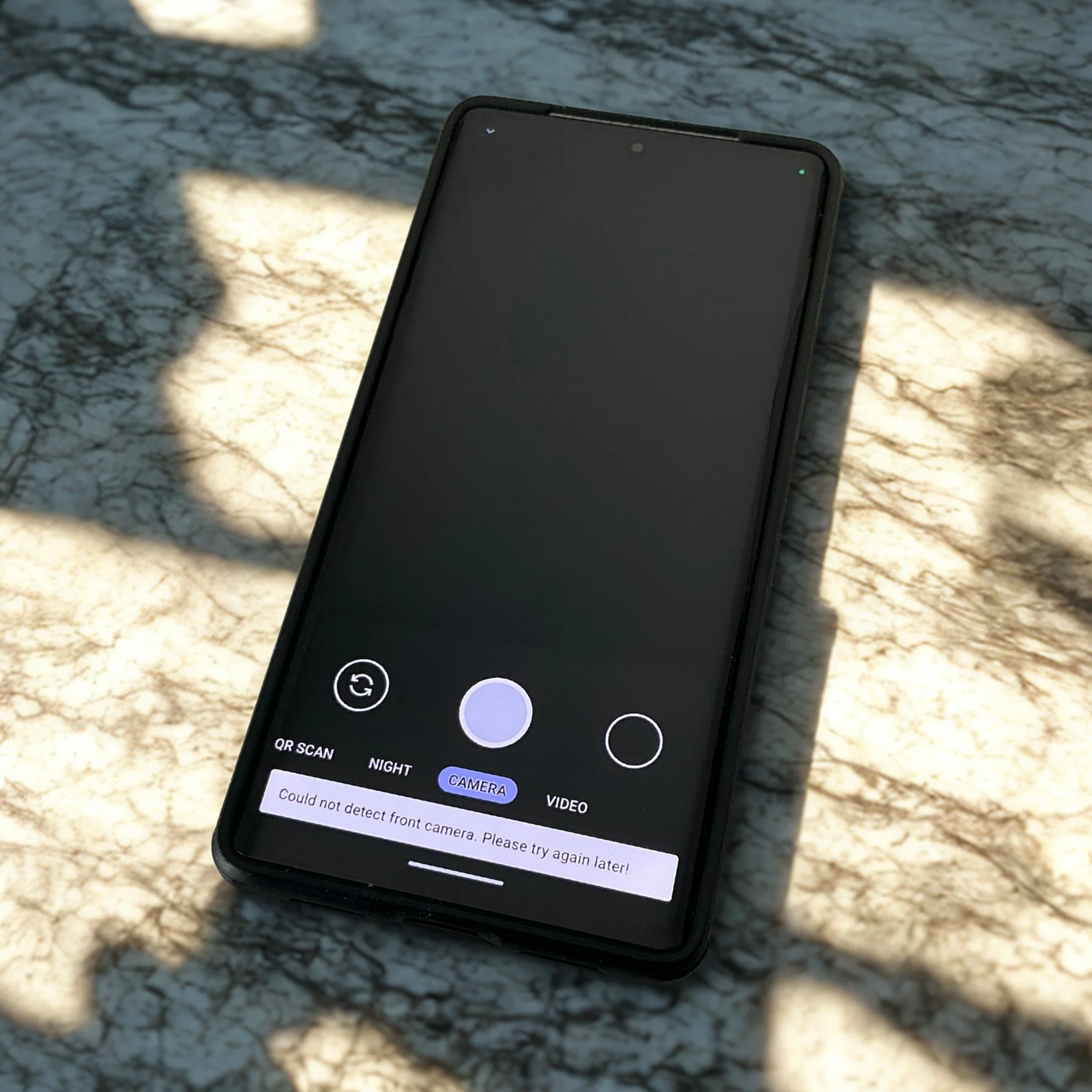
What happens when you’re forced to unlock your phone? This is where the duress PIN and panic actions come into play. These features are not just about hiding your data; they are about protecting it actively.
Imagine this: You’re in a situation where you’re pressured to unlock your device. By using a special PIN, your phone can trigger panic actions, such as wiping sensitive information or activating a lockdown of certain apps. This ensures your data remains safe, even when you’re not in control. It’s a proactive measure that gives you the upper hand, reinforcing your right to privacy.
Metadata Minimisation Techniques
It’s not just the content on your phone that’s at risk. Metadata, such as location and communication patterns, can reveal a lot about you. Most users overlook this, but metadata can be just as compromising as direct data.
Privacy Devices employs techniques to minimise metadata exposure. This means your phone is configured to reduce the trails you leave behind. With secure mobile configuration, your device shields your activities, keeping prying eyes at bay. It’s a silent guardian, ensuring your digital footprint remains yours alone.
Real-World Applications

These advanced solutions are not theoretical; they have practical uses for individuals facing real threats.
Mobile Security for Journalists
Journalists often work in high-risk areas where privacy is essential. A privacy-focused phone is crucial here. These devices offer mobile security for journalists, ensuring their sources and information remain confidential.
In the field, a typical smartphone can be a liability. With features like Mullvad VPN on mobile and secure communications, journalists can report without fear of exposure. This empowers them to do their job without compromising their integrity or safety.
Executive Device Protection
Executives deal with sensitive data daily. A secure communications device is vital to protect proprietary information. Without it, the risk of data breaches is significant.
For executives, the stakes are high. A verified boot smartphone ensures that every startup is secure, protecting against tampering. This level of protection is not just beneficial; it is essential for maintaining competitive advantage and trust.
High-Stakes Environment Strategies
In high-stakes environments, every decision counts. Privacy devices offer strategies that ensure you stay ahead of threats. From secure mobile configuration to metadata minimisation, these solutions are tailored to meet the demands of challenging situations.
The longer you wait to adopt these strategies, the greater the risk to your data. Don’t leave your privacy to chance. Protect it with a device designed to safeguard your information even in the toughest conditions.
By focusing on privacy by design, Privacy Devices offers a lifeline to those who need it most. Whether you’re a journalist, an executive, or anyone operating in high-risk environments, having the right tools is not a luxury; it’s a necessity. Secure your data, maintain your privacy, and embrace a future where your information is truly yours.