Fail‑Safe Mobile Configurations for Journalists and Privacy Professionals
Standard smartphones crumble the moment you face loss, seizure, or coercion. Your sensitive data is exposed, your privacy shattered. Custom security configurations built on hardened mobile foundations like GrapheneOS are designed to withstand real-world attacks and protect your communications. In this post, you’ll learn how tailored setups with duress PINs, metadata minimisation, and compartmentalisation keep your data locked down when it matters most. For more information, check out this digital privacy guide for journalists and PR specialists.
Tailored Security for High-Risk Environments
In high-stakes scenarios, your mobile device should be your strongest ally. Custom security configurations ensure it stands ready to protect, regardless of the threat. Let’s explore what these configurations entail and why they matter.
Custom Mobile Configurations Explained
Think of custom mobile configurations as a personal security detail for your smartphone. They are crafted to anticipate risks you may face, such as monitoring or coercion. At their core, these setups use open-source security systems like GrapheneOS and AOSP, providing a robust defence against common and complex threats. Each detail matters, from duress PINs to panic actions, ensuring your data remains out of reach when under pressure. With tailored configurations, your device is not just smart, it’s proactive in safeguarding your privacy.
Importance of Hardened Mobile Systems
Why settle for standard when the stakes are high? Hardened mobile systems are built to withstand real-world threats that conventional devices can’t handle. They offer more than just basic security settings. They are designed to handle extreme scenarios, keeping your data safe during seizures or enforced access attempts. This kind of resilience is essential for journalists, executives, and anyone needing reliable protection in uncertain environments. The need for such systems is rising, as digital threats become more sophisticated, making them an indispensable tool for safeguarding privacy.
Key Features of Hardened Mobile Systems

Diving deeper, we uncover the game-changing features that set these systems apart. Each element plays a critical role in maintaining your privacy under duress.
Duress PIN and Panic Actions
Imagine a scenario where you must surrender your device. This is where a duress PIN comes into play. It’s different from your normal code and triggers predetermined actions, like wiping sensitive information. Panic actions allow for rapid, irreversible data loss, ensuring nothing vital falls into the wrong hands. Such features are pivotal in keeping your data safe during unexpected situations, acting as your digital safety net. They are simple to set up, yet incredibly effective in executing complex security protocols instantly.
Metadata Minimisation and Compartmentalisation
Every digital move you make leaves a trace, but metadata minimisation ensures these traces are few and far between. By limiting the data your device records, you reduce your digital footprint significantly. Compartmentalisation further protects by segregating data, preventing cross-access between apps and functions. This means your personal and professional information remains separate, and breaches in one area won’t compromise the other. Together, these methods provide a formidable defence against data exposure.
Secure Communications and SIM Hygiene
Your communication channels are the lifelines to your privacy. Ensuring they are secure is crucial. Secure communications utilise encryption to protect your conversations from prying eyes. Coupled with SIM hygiene, which involves simple practices like regularly changing SIM cards, you maintain control over who accesses your network. These strategies collectively shield your communications, ensuring your messages are heard only by those intended. It’s an ongoing process of vigilance, but it is essential in a world where digital eavesdropping is all too common.
Practical Benefits for Journalists and Privacy Professionals

Now, let’s see how these features translate into real-world benefits, particularly for those on the front lines of privacy protection.
Enhanced Journalist Security and Device Seizure Defence
Journalists often find themselves in risky situations where device seizure defence is critical. Hardened mobile configurations minimise exposure if devices are confiscated. This protection allows journalists to focus on their stories, not the safety of their data. By utilising these systems, they possess a reliable defence against unwanted access, ensuring their sources and work remain confidential. If you’re a journalist, this kind of security isn’t just an option; it’s a necessity.
Coercion Resistance and Secure Messaging
In high-pressure situations, maintaining control over your device is vital. Features like coercion resistance provide a safeguard against forced access, ensuring your data integrity even under duress. Secure messaging apps further protect your communications, encrypting every message you send. These tools let you navigate challenging scenarios with confidence, knowing your information remains secure. They are particularly crucial for privacy professionals who need to ensure their conversations are never compromised.
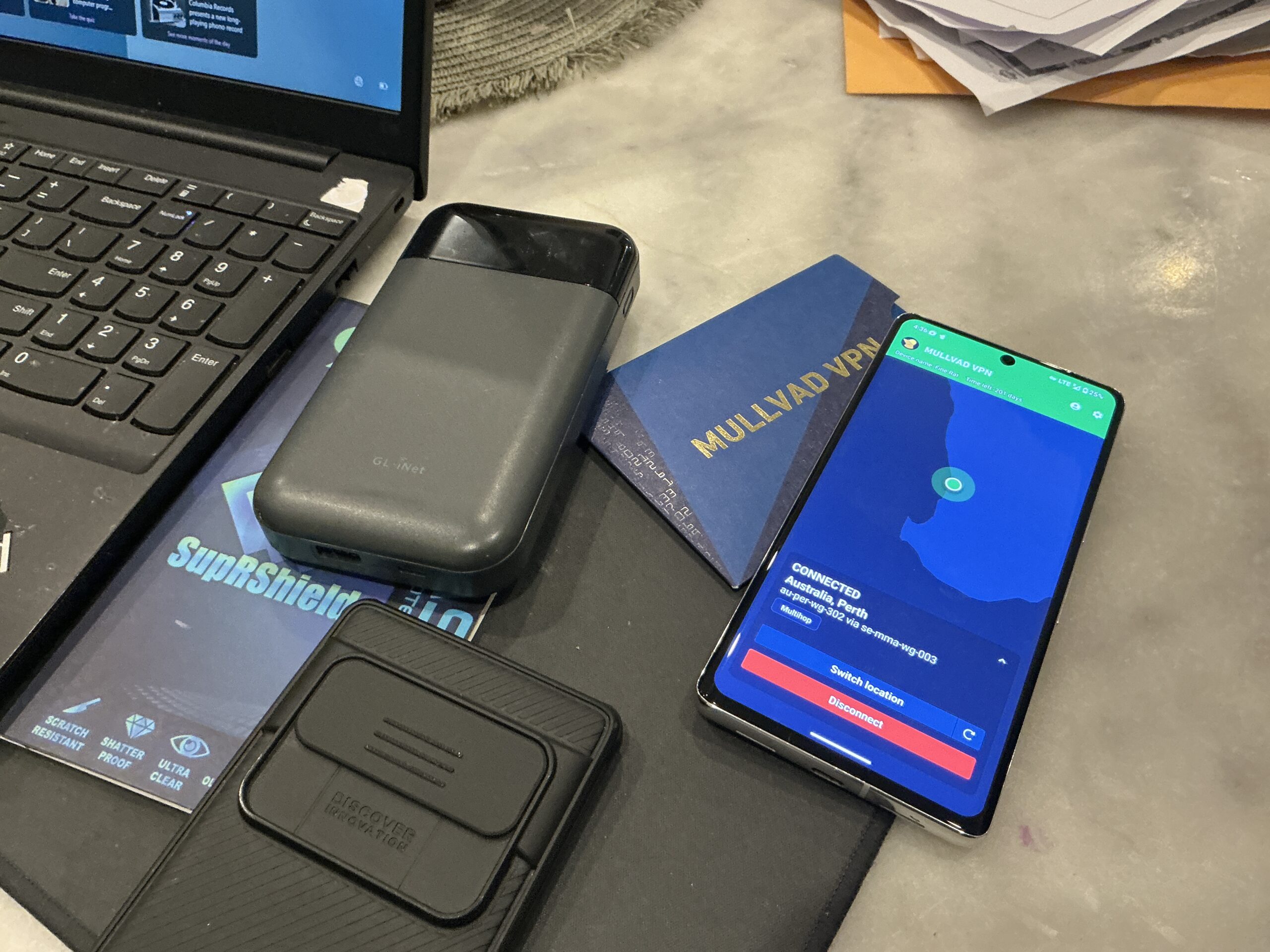
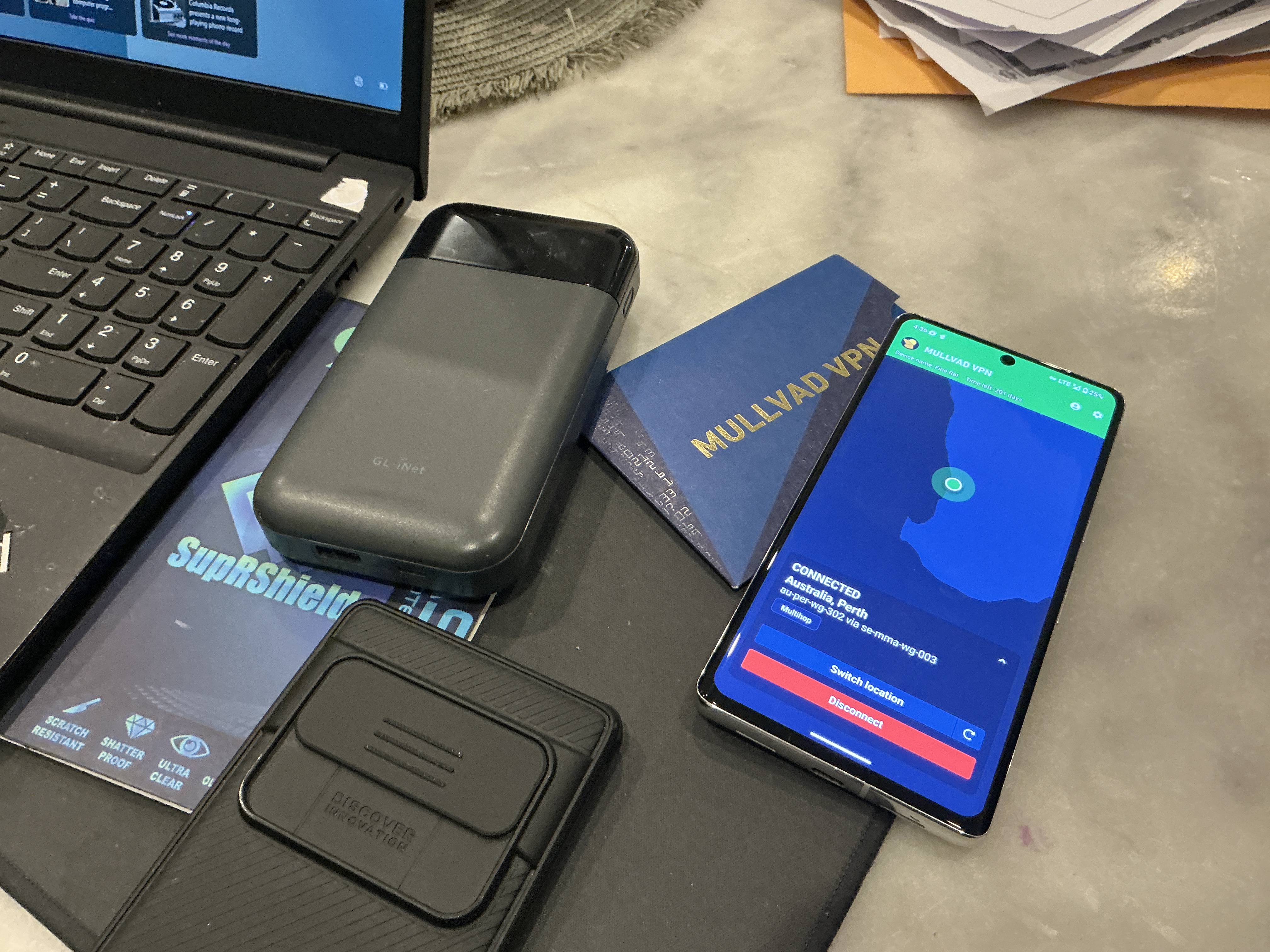
Mobile Hardening in Australia: Privacy by Design
Australia’s landscape demands a proactive approach to mobile security. Mobile hardening Australia is all about integrating privacy from the ground up, rather than treating it as an afterthought. This approach, known as privacy by design, ensures that every aspect of your mobile system considers your privacy first. It’s a forward-thinking method that anticipates threats and provides enduring solutions. As digital landscapes evolve, staying ahead with such strategies becomes not only wise but essential.
In a world where digital privacy is constantly under threat, these specialised mobile configurations offer an essential shield. They empower you to operate fearlessly, knowing your data is secure, even in unpredictable situations. Equip yourself with the right tools, and take control of your digital world.